
Terrorist attacks have heightened our awareness of security, although most day-to-day risk is from lower-impact threats, Simon White and Douglas Cochrane from consultancy Control Risks explain how to integrate it from the start.
Security threats to the built environment in the United Kingdom are constantly evolving. In the 1970s and 1980s, the Irish Republican Army (IRA) targeted iconic infrastructure with large explosive devices. Later, in the 2000s, international terrorist groups targeted crowded spaces.
More recently, with the attacks such as those in Paris in 2015, Nice and Berlin in 2016, and London and Manchester this year, there has been a prevalence of, predominantly, marauding firearms and “vehicle as weapon” attacks.
But while many people perceive terrorism as the key security threat to built infrastructure in the UK, higher probability yet lower-impact threats such as criminality, mass protest and anti-social behaviour require equal consideration.
Despite this, security is fairly low down the priority list for the majority of developers working outside of defence or critical national infrastructure projects. It is often seen as a dirty word or an additional expense. Although it is understood to be a project requirement, it is never viewed as a project priority and is rarely incorporated beyond what is absolutely necessary.
However, having a proportionate, holistic security strategy and pragmatic design presents considerable benefits to any development. Most importantly, a scalable and adaptable security infrastructure will allow developments to respond to emerging threats.
Adding value to a development
Although the benefits of security may not be immediately apparent, a coherent security design can add real value to a development in the long term. A secure building does not need to look unsightly, as is the case with many retro-fitted security measures.
Instead, incorporating security during the design process means that security needs can be seamlessly integrated into the building, allowing it to operate efficiently yet securely. This will satisfy the security due-diligence questions of prospective purchasers, increase marketability and push up rental values.
It also has the potential to reduce insurance premiums and – perhaps most importantly – satisfy the duty of care requirements of developers and employers.
Weighing up requirements
So where do you start? Basic design requirements may be stipulated by planning conditions. Some local authorities, for example, require Secured by Design certification, and security requirements on residential projects that commenced after October 2015 will be guided by Approved Document Q (Security).
For developments that face a potential terrorism threat, it is likely that a police counter terrorism security adviser (CTSA) will have to be consulted.
Schemes that are seeking Building Research Establishment Environmental Assessment Method (BREEAM) accreditation or that of the now abolished Code for Sustainable Homes (CfSH), can pick up credits for accounting for security considerations in the overall design of the development – which essentially means following the principles of Secured by Design.

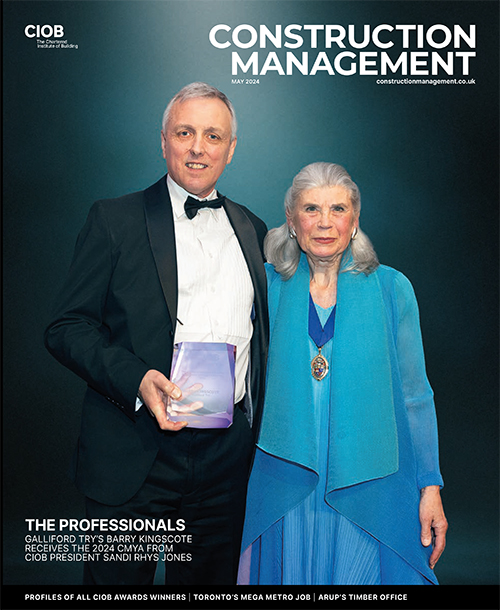
Security measures that are designed into structures from the outset can prevent the need to retro-fit protective measures such as these steel barriers and concrete blocks that were installed in June on Westminster Bridge following recent terrorist attacks
But where security is enforced in such a manner, it can become inappropriate, oversized or ill-fitting. Tailored consideration for security from the early stages of the design process is almost exclusively only seen when a building has been developed for an end user directly or by a well-informed developer.
While schemes such as Secured by Design are extremely effective in the residential and education sectors, they become less relevant in prime residential or high-end commercial office developments and may adversely impact design. Developers in these sectors rarely put value on the Secured by Design badge.
Importantly, the Secured by Design process doesn’t emphasise the need for a site-specific security threat and risk assessment and, as such, the one-size-fits-all tick-box approach doesn’t necessarily facilitate proportionate, risk-commensurate security design.
To ensure risk-commensurate design, it is vital to understand the security threats likely to be faced at the earliest opportunity. The BREEAM credit requires an appropriately experienced security consultant to conduct an evidence-based security needs assessment (SNA), also known as a security threat and risk assessment, during or prior to concept design in RIBA Stage 2.
Read related articles
‘This was not just another building opening’
Sky fence stops drones flying over prison
In a recent survey of architects, developers, investors and end users conducted by Control Risks, 74% of respondents said they considered it essential to conduct a threat and risk assessment at the conceptual design stage. In reality, however, it is often conducted too late, or not at all.
The assessment should concisely spell out the threats and estimate their likelihood and impact by using credible data and experience. Too often, however, they become overly long documents that tend to offer no firm conclusions. This is where the experience of the security consultant adds value to the process by identifying and analysing the key risks, rather than trying to address every possible threat.
To make the threat and risk assessment even more relevant, stakeholders such as architectural liaison officers (ALOs) or designing out crime officers (DOCOs) should be consulted and their recommendations recorded for future reference – particularly as this is a CfSH requirement. If the project requires consultation with the local CTSA, then it is useful to present the assessment to them to gain their support.
Whether or not a development is seeking the BREEAM or CfSH credit for security, following this threat and risk assessment process will apply logic and reasoning to all future security design decisions.
Understand your tolerance to risk
How do you apply the security threat and risk assessment? Each of the individual risks identified during the assessment process needs to be considered and an informed “responsible person” needs to decide how much investment they are prepared to make in order to reduce the risk to a tolerable level.
“The experience of the security consultant adds value by identifying and analysing the key risks, rather than trying to address every possible threat.”
An extreme case, for example, would be a new building in a location with a greater probability of being targeted by terrorists using explosives, either directly or as a collateral target – an example would be a development near an iconic government building or high-profile foreign embassy.
If the new building incorporates no structural blast enhancements then the impact of a local explosive attack may result in facade damage, significant glazing failure, or even partial collapse of the building. Depending on the expected occupancy, there could be casualties.
A developer or end user with a very high risk-tolerance may be able to accept that impact and therefore invest little in the design to reduce it. Those with a very low risk-tolerance would invest resources to design the building to withstand such potential events.
This is a very contentious subject and one that is not very well understood – particularly as end users are often unwilling to formally approve acceptance of an increased risk profile. For a developer, it is an even more challenging decision that could have considerable financial implications. Consequently it requires input from the marketing team, cost consultants and the design team.
In the same Control Risks survey mentioned earlier, 61% of respondents admitted to having a “good” or “very good” understanding of their tolerable loss. Ultimately, the “responsible person” needs to make a decision, whatever it may be, on an informed basis with a clear rationale. The decision should also be suitably documented through an auditable process. A security consultant can help articulate the possible eventualities of such decisions.
Who should you engage with?
The security threat and risk assessment, and subsequent security strategy and design, need to be produced by an appropriately experienced security consultant. This should be someone with experience in the construction industry and who understands the intricacies of physical and electronic security standards, as well as the challenges of security systems procurement.
One option is to engage a member of the Register of Security Engineers and Specialists (RSES), which is a scheme sponsored by the Centre for the Protection of National Infrastructure (CPNI) and administered by the Institution of Civil Engineers (ICE). This offers potential clients and insurers the assurance that members have achieved a recognised competence standard through a professional review process.
As part of this process, it is imperative that the high-level security requirements are proportional and risk-commensurate. Once these requirements have been established, they will be used as the basis for the design of the whole project.
Any future departure from these requirements should be justified and recorded by the security consultant, not least so that the tolerable loss stance taken by the company can be justified in case it is subsequently challenged.
During the developed design stage, recognised physical and electronic security design standards should be established and implemented in the design. These include standards such as BS EN 356 for glazing security or LPS 1175 for physical security. The standards applied need to be based on the requirements identified by the assessment, which in turn will allow security protection levels to be quantifiable and the process for developing these levels to be auditable.
Simon White is director of security design and engineering and Douglas Cochrane is senior security design consultant at independent global risk consultancy Control Risks

Four steps to better security through design
Design teams are recommended to follow these processes to incorporate security design into projects:
1. Consider security early
Consider the security requirements during RIBA Stage 2, or earlier if possible. If security design requirements are considered early and collaboratively, the financial burden of incorporating security infrastructure can be minimised through integrated and efficient design.
The architectural impact of security infrastructure can also be lessened, along with the avoidance of costly and unsightly retro-fitted security measures.
2. Be aware of risk tolerance
Understand the threat and end-user risk tolerance. Produce a project-specific security threat and risk assessment that engages all stakeholders including the client, architect, architectural liaison officer or designing out crime officer and counter terrorism security adviser.
The assessment needs to be presented to the client in order to achieve their buy-in and to establish their risk tolerance. This then forms the basis of the security concept design.
3. Create scalable security infrastructure
Things change – a security threat may increase or a future tenant may have a much lower security risk tolerance, and only be willing to sign a lease if certain measures are introduced. If these enhancements can be readily made without significant works, then the development will become much more attractive to end users.
4. Take a holistic approach
Understand that there is no single solution to security challenges. Physical measures such as hostile vehicle barriers, blast-resistant glazing and secure building perimeters have their place, as do advanced electronic solutions such as video surveillance, intrusion detection, advanced baggage scanning and video analytics.
But these will not be effective without being combined with appropriate operational procedures and suitable security and incident response plans and personnel.
Using this approach will enable effective and aesthetic security solutions to become an integral part of a construction project. This will maximise responsiveness to evolving security threats and add value in an
already competitive property market.







Comments are closed.